Page 93 - Cyber Defense eMagazine October 2023
P. 93
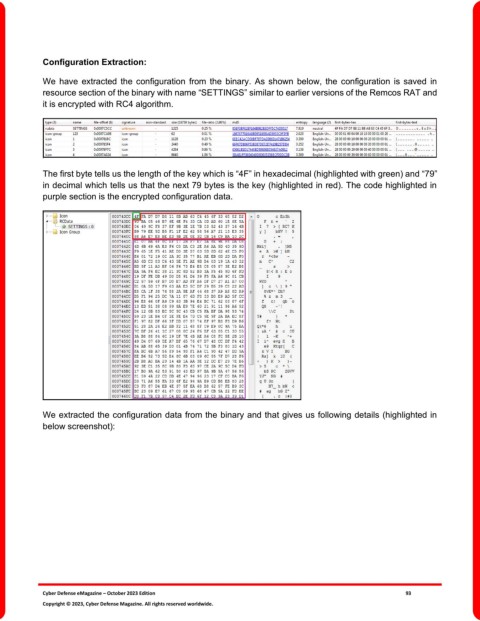
Configuration Extraction:
We have extracted the configuration from the binary. As shown below, the configuration is saved in
resource section of the binary with name “SETTINGS” similar to earlier versions of the Remcos RAT and
it is encrypted with RC4 algorithm.
The first byte tells us the length of the key which is “4F” in hexadecimal (highlighted with green) and “79”
in decimal which tells us that the next 79 bytes is the key (highlighted in red). The code highlighted in
purple section is the encrypted configuration data.
We extracted the configuration data from the binary and that gives us following details (highlighted in
below screenshot):
Cyber Defense eMagazine – October 2023 Edition 93
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.