Page 94 - Cyber Defense eMagazine October 2023
P. 94
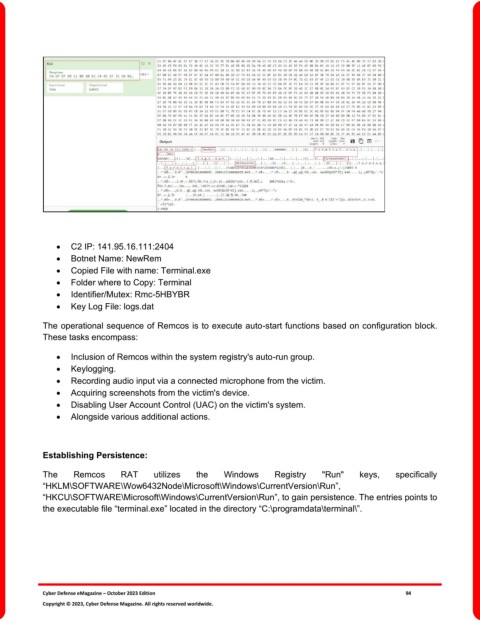
• C2 IP: 141.95.16.111:2404
• Botnet Name: NewRem
• Copied File with name: Terminal.exe
• Folder where to Copy: Terminal
• Identifier/Mutex: Rmc-5HBYBR
• Key Log File: logs.dat
The operational sequence of Remcos is to execute auto-start functions based on configuration block.
These tasks encompass:
• Inclusion of Remcos within the system registry's auto-run group.
• Keylogging.
• Recording audio input via a connected microphone from the victim.
• Acquiring screenshots from the victim's device.
• Disabling User Account Control (UAC) on the victim's system.
• Alongside various additional actions.
Establishing Persistence:
The Remcos RAT utilizes the Windows Registry "Run" keys, specifically
“HKLM\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run”,
“HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Run”, to gain persistence. The entries points to
the executable file “terminal.exe” located in the directory “C:\programdata\terminal\”.
Cyber Defense eMagazine – October 2023 Edition 94
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.