Page 96 - Cyber Defense eMagazine October 2023
P. 96
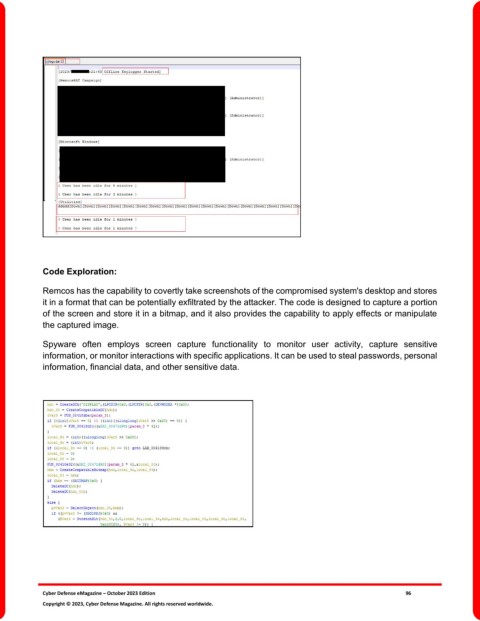
Code Exploration:
Remcos has the capability to covertly take screenshots of the compromised system's desktop and stores
it in a format that can be potentially exfiltrated by the attacker. The code is designed to capture a portion
of the screen and store it in a bitmap, and it also provides the capability to apply effects or manipulate
the captured image.
Spyware often employs screen capture functionality to monitor user activity, capture sensitive
information, or monitor interactions with specific applications. It can be used to steal passwords, personal
information, financial data, and other sensitive data.
Cyber Defense eMagazine – October 2023 Edition 96
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.