Page 98 - Cyber Defense eMagazine October 2023
P. 98
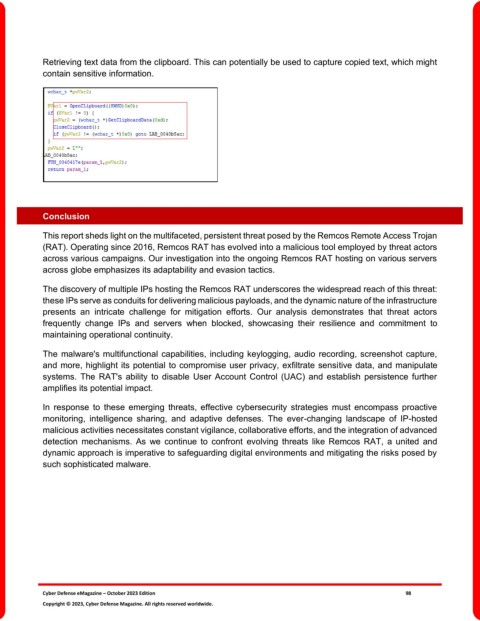
Retrieving text data from the clipboard. This can potentially be used to capture copied text, which might
contain sensitive information.
Conclusion
This report sheds light on the multifaceted, persistent threat posed by the Remcos Remote Access Trojan
(RAT). Operating since 2016, Remcos RAT has evolved into a malicious tool employed by threat actors
across various campaigns. Our investigation into the ongoing Remcos RAT hosting on various servers
across globe emphasizes its adaptability and evasion tactics.
The discovery of multiple IPs hosting the Remcos RAT underscores the widespread reach of this threat:
these IPs serve as conduits for delivering malicious payloads, and the dynamic nature of the infrastructure
presents an intricate challenge for mitigation efforts. Our analysis demonstrates that threat actors
frequently change IPs and servers when blocked, showcasing their resilience and commitment to
maintaining operational continuity.
The malware's multifunctional capabilities, including keylogging, audio recording, screenshot capture,
and more, highlight its potential to compromise user privacy, exfiltrate sensitive data, and manipulate
systems. The RAT's ability to disable User Account Control (UAC) and establish persistence further
amplifies its potential impact.
In response to these emerging threats, effective cybersecurity strategies must encompass proactive
monitoring, intelligence sharing, and adaptive defenses. The ever-changing landscape of IP-hosted
malicious activities necessitates constant vigilance, collaborative efforts, and the integration of advanced
detection mechanisms. As we continue to confront evolving threats like Remcos RAT, a united and
dynamic approach is imperative to safeguarding digital environments and mitigating the risks posed by
such sophisticated malware.
Cyber Defense eMagazine – October 2023 Edition 98
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.