Page 88 - Cyber Defense eMagazine October 2023
P. 88
Changing Infrastructure and Tactics Over Time:
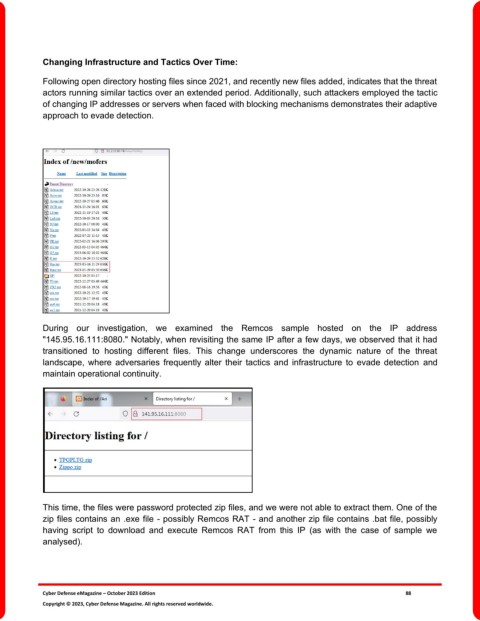
Following open directory hosting files since 2021, and recently new files added, indicates that the threat
actors running similar tactics over an extended period. Additionally, such attackers employed the tactic
of changing IP addresses or servers when faced with blocking mechanisms demonstrates their adaptive
approach to evade detection.
During our investigation, we examined the Remcos sample hosted on the IP address
"145.95.16.111:8080." Notably, when revisiting the same IP after a few days, we observed that it had
transitioned to hosting different files. This change underscores the dynamic nature of the threat
landscape, where adversaries frequently alter their tactics and infrastructure to evade detection and
maintain operational continuity.
This time, the files were password protected zip files, and we were not able to extract them. One of the
zip files contains an .exe file - possibly Remcos RAT - and another zip file contains .bat file, possibly
having script to download and execute Remcos RAT from this IP (as with the case of sample we
analysed).
Cyber Defense eMagazine – October 2023 Edition 88
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.