Page 90 - Cyber Defense eMagazine October 2023
P. 90
Variety of Hosted Files:
Other files hosted on the IP address "141[.]95[.]16[.]111:8080" include:
• "newpy.exe" (b28167faf2bcf0150d5e816346abb42d): A variant of Remcos RAT, known for its
remote control and surveillance capabilities.
• "echo-4662-2DF5.exe" (25fca21c810a8ffabf4fdf3b1755c73c): Abused version of "echo.exe," a
utility used for identifying cheaters in gaming environments. The inclusion of this file suggests a
potential focus on the gaming industry or individuals affiliated with gaming.
• Web page (ec): Crafted to mimic the official interface of the "echo" utility, serving as a deceptive
element to mislead users into interacting with it.
• "123.exe" (791545E6E3C5EB61DD12CCFBAE1B9982): This file is abused version of the
Windows command line processor utility "cmd.exe," reflecting threat actors' exploitation of
legitimate utilities for potentially malicious activities. The abuse of such utilities provides
cybercriminals with a cloak of authenticity, allowing them to evade suspicion and blend in with
standard system processes.
• Two image files (abc.png, pp258.ico): While these image files might appear benign, they could
serve as decoys to distract from the presence of more malicious content or methods.
The hosting of abused versions of legitimate utilities like “echo.exe” and “cmd.exe” indicates repurposing
them to serve malicious objectives. This tactic allows them to camouflage their activities within the façade
of trusted software. The diversity of files hosted on the IP suggests a multi-pronged approach by threat
actors, utilizing both well-known tools and seemingly harmless content to mask their intentions.
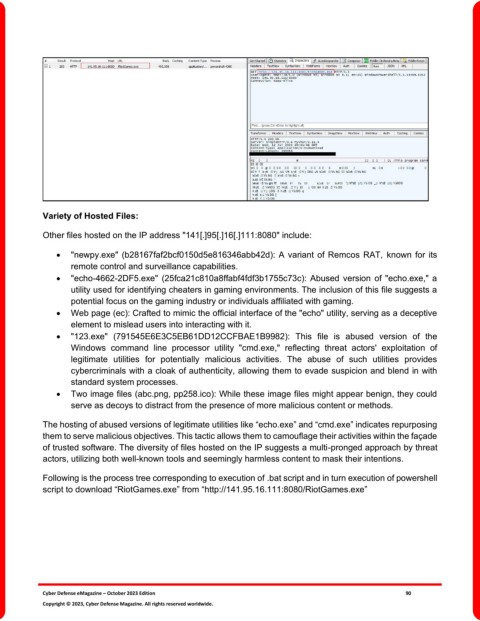
Following is the process tree corresponding to execution of .bat script and in turn execution of powershell
script to download “RiotGames.exe” from “http://141.95.16.111:8080/RiotGames.exe”
Cyber Defense eMagazine – October 2023 Edition 90
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.