Page 78 - Cyber Defense eMagazine September 2023
P. 78
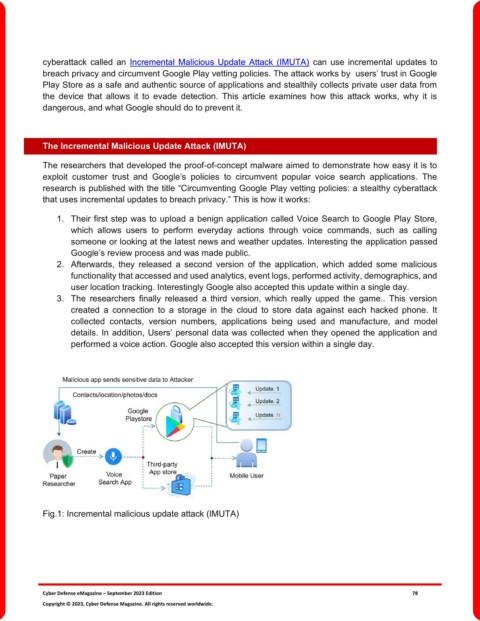
cyberattack called an Incremental Malicious Update Attack (IMUTA) can use incremental updates to
breach privacy and circumvent Google Play vetting policies. The attack works by users’ trust in Google
Play Store as a safe and authentic source of applications and stealthily collects private user data from
the device that allows it to evade detection. This article examines how this attack works, why it is
dangerous, and what Google should do to prevent it.
The Incremental Malicious Update Attack (IMUTA)
The researchers that developed the proof-of-concept malware aimed to demonstrate how easy it is to
exploit customer trust and Google’s policies to circumvent popular voice search applications. The
research is published with the title “Circumventing Google Play vetting policies: a stealthy cyberattack
that uses incremental updates to breach privacy.” This is how it works:
1. Their first step was to upload a benign application called Voice Search to Google Play Store,
which allows users to perform everyday actions through voice commands, such as calling
someone or looking at the latest news and weather updates. Interesting the application passed
Google’s review process and was made public.
2. Afterwards, they released a second version of the application, which added some malicious
functionality that accessed and used analytics, event logs, performed activity, demographics, and
user location tracking. Interestingly Google also accepted this update within a single day.
3. The researchers finally released a third version, which really upped the game.. This version
created a connection to a storage in the cloud to store data against each hacked phone. It
collected contacts, version numbers, applications being used and manufacture, and model
details. In addition, Users’ personal data was collected when they opened the application and
performed a voice action. Google also accepted this version within a single day.
Fig.1: Incremental malicious update attack (IMUTA)
Cyber Defense eMagazine – September 2023 Edition 78
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.