Page 92 - Cyber Defense eMagazine August 2023
P. 92
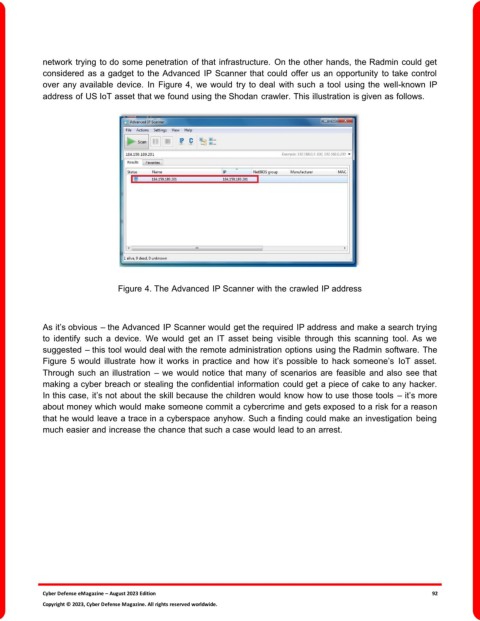
network trying to do some penetration of that infrastructure. On the other hands, the Radmin could get
considered as a gadget to the Advanced IP Scanner that could offer us an opportunity to take control
over any available device. In Figure 4, we would try to deal with such a tool using the well-known IP
address of US IoT asset that we found using the Shodan crawler. This illustration is given as follows.
Figure 4. The Advanced IP Scanner with the crawled IP address
As it’s obvious – the Advanced IP Scanner would get the required IP address and make a search trying
to identify such a device. We would get an IT asset being visible through this scanning tool. As we
suggested – this tool would deal with the remote administration options using the Radmin software. The
Figure 5 would illustrate how it works in practice and how it’s possible to hack someone’s IoT asset.
Through such an illustration – we would notice that many of scenarios are feasible and also see that
making a cyber breach or stealing the confidential information could get a piece of cake to any hacker.
In this case, it’s not about the skill because the children would know how to use those tools – it’s more
about money which would make someone commit a cybercrime and gets exposed to a risk for a reason
that he would leave a trace in a cyberspace anyhow. Such a finding could make an investigation being
much easier and increase the chance that such a case would lead to an arrest.
Cyber Defense eMagazine – August 2023 Edition 92
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.