Page 130 - Cyber Defense eMagazine October 2023
P. 130
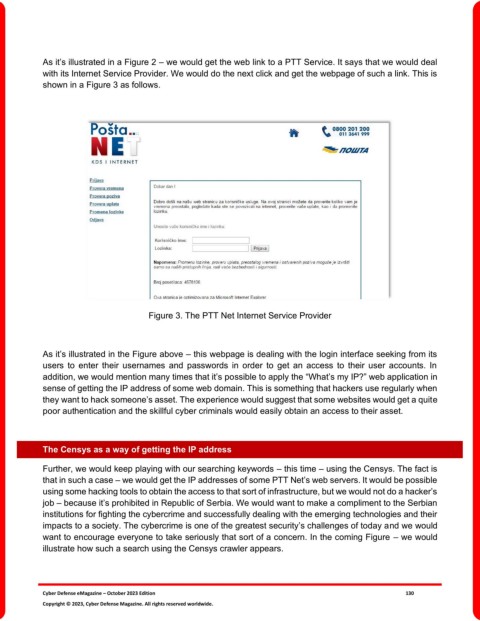
As it’s illustrated in a Figure 2 – we would get the web link to a PTT Service. It says that we would deal
with its Internet Service Provider. We would do the next click and get the webpage of such a link. This is
shown in a Figure 3 as follows.
Figure 3. The PTT Net Internet Service Provider
As it’s illustrated in the Figure above – this webpage is dealing with the login interface seeking from its
users to enter their usernames and passwords in order to get an access to their user accounts. In
addition, we would mention many times that it’s possible to apply the “What’s my IP?” web application in
sense of getting the IP address of some web domain. This is something that hackers use regularly when
they want to hack someone’s asset. The experience would suggest that some websites would get a quite
poor authentication and the skillful cyber criminals would easily obtain an access to their asset.
The Censys as a way of getting the IP address
Further, we would keep playing with our searching keywords – this time – using the Censys. The fact is
that in such a case – we would get the IP addresses of some PTT Net’s web servers. It would be possible
using some hacking tools to obtain the access to that sort of infrastructure, but we would not do a hacker’s
job – because it’s prohibited in Republic of Serbia. We would want to make a compliment to the Serbian
institutions for fighting the cybercrime and successfully dealing with the emerging technologies and their
impacts to a society. The cybercrime is one of the greatest security’s challenges of today and we would
want to encourage everyone to take seriously that sort of a concern. In the coming Figure – we would
illustrate how such a search using the Censys crawler appears.
Cyber Defense eMagazine – October 2023 Edition 130
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.