Page 86 - Cyber Defense eMagazine March 2024
P. 86
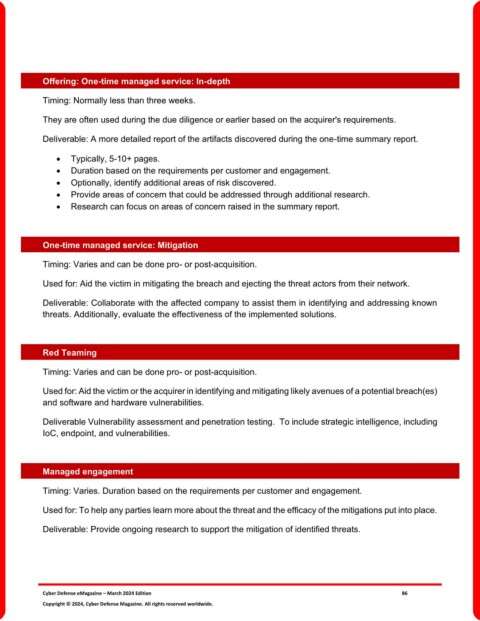
Offering: One-time managed service: In-depth
Timing: Normally less than three weeks.
They are often used during the due diligence or earlier based on the acquirer's requirements.
Deliverable: A more detailed report of the artifacts discovered during the one-time summary report.
• Typically, 5-10+ pages.
• Duration based on the requirements per customer and engagement.
• Optionally, identify additional areas of risk discovered.
• Provide areas of concern that could be addressed through additional research.
• Research can focus on areas of concern raised in the summary report.
One-time managed service: Mitigation
Timing: Varies and can be done pro- or post-acquisition.
Used for: Aid the victim in mitigating the breach and ejecting the threat actors from their network.
Deliverable: Collaborate with the affected company to assist them in identifying and addressing known
threats. Additionally, evaluate the effectiveness of the implemented solutions.
Red Teaming
Timing: Varies and can be done pro- or post-acquisition.
Used for: Aid the victim or the acquirer in identifying and mitigating likely avenues of a potential breach(es)
and software and hardware vulnerabilities.
Deliverable Vulnerability assessment and penetration testing. To include strategic intelligence, including
IoC, endpoint, and vulnerabilities.
Managed engagement
Timing: Varies. Duration based on the requirements per customer and engagement.
Used for: To help any parties learn more about the threat and the efficacy of the mitigations put into place.
Deliverable: Provide ongoing research to support the mitigation of identified threats.
Cyber Defense eMagazine – March 2024 Edition 86
Copyright © 2024, Cyber Defense Magazine. All rights reserved worldwide.