Page 45 - Cyber Defense eMagazine for July 2020
P. 45
It is impossible to know whether John would have committed an act of sabotage or self-harm, but the
mitigation efforts nevertheless reduced the chances and allowed John to remain employed and
productive.
Without a proactive response, the alternative is to detect and respond to an event after it occurs, incurring
the cost of the impact then attempting to minimize the effect.
The Path to Proactive Risk Mitigation
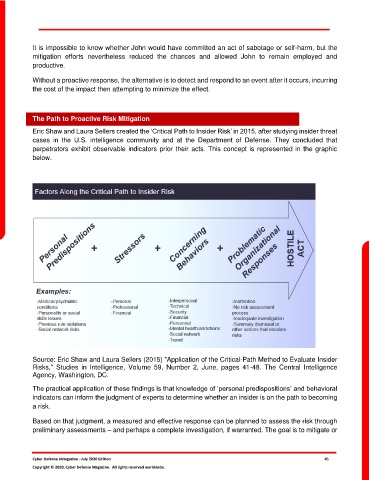
Eric Shaw and Laura Sellers created the ‘Critical Path to Insider Risk’ in 2015, after studying insider threat
cases in the U.S. intelligence community and at the Department of Defense. They concluded that
perpetrators exhibit observable indicators prior their acts. This concept is represented in the graphic
below.
Source: Eric Shaw and Laura Sellers (2015) "Application of the Critical-Path Method to Evaluate Insider
Risks," Studies in Intelligence, Volume 59, Number 2, June, pages 41-48. The Central Intelligence
Agency, Washington, DC.
The practical application of these findings is that knowledge of ‘personal predispositions’ and behavioral
indicators can inform the judgment of experts to determine whether an insider is on the path to becoming
a risk.
Based on that judgment, a measured and effective response can be planned to assess the risk through
preliminary assessments – and perhaps a complete investigation, if warranted. The goal is to mitigate or
Cyber Defense eMagazine –July 2020 Edition 45
Copyright © 2020, Cyber Defense Magazine. All rights reserved worldwide.