Page 82 - Cyber Defense eMagazine August 2023
P. 82
1. Review Shared Responsibility Matrix in the Public Cloud
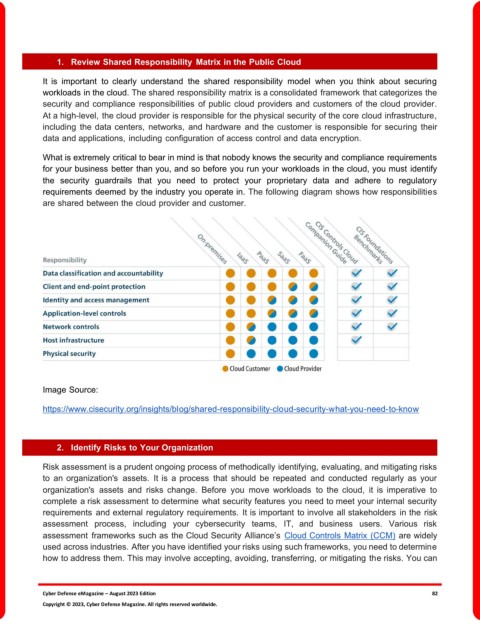
It is important to clearly understand the shared responsibility model when you think about securing
workloads in the cloud. The shared responsibility matrix is a consolidated framework that categorizes the
security and compliance responsibilities of public cloud providers and customers of the cloud provider.
At a high-level, the cloud provider is responsible for the physical security of the core cloud infrastructure,
including the data centers, networks, and hardware and the customer is responsible for securing their
data and applications, including configuration of access control and data encryption.
What is extremely critical to bear in mind is that nobody knows the security and compliance requirements
for your business better than you, and so before you run your workloads in the cloud, you must identify
the security guardrails that you need to protect your proprietary data and adhere to regulatory
requirements deemed by the industry you operate in. The following diagram shows how responsibilities
are shared between the cloud provider and customer.
Image Source:
https://www.cisecurity.org/insights/blog/shared-responsibility-cloud-security-what-you-need-to-know
2. Identify Risks to Your Organization
Risk assessment is a prudent ongoing process of methodically identifying, evaluating, and mitigating risks
to an organization's assets. It is a process that should be repeated and conducted regularly as your
organization's assets and risks change. Before you move workloads to the cloud, it is imperative to
complete a risk assessment to determine what security features you need to meet your internal security
requirements and external regulatory requirements. It is important to involve all stakeholders in the risk
assessment process, including your cybersecurity teams, IT, and business users. Various risk
assessment frameworks such as the Cloud Security Alliance’s Cloud Controls Matrix (CCM) are widely
used across industries. After you have identified your risks using such frameworks, you need to determine
how to address them. This may involve accepting, avoiding, transferring, or mitigating the risks. You can
Cyber Defense eMagazine – August 2023 Edition 82
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.