Page 44 - Cyber Defense eMagazine August 2023
P. 44
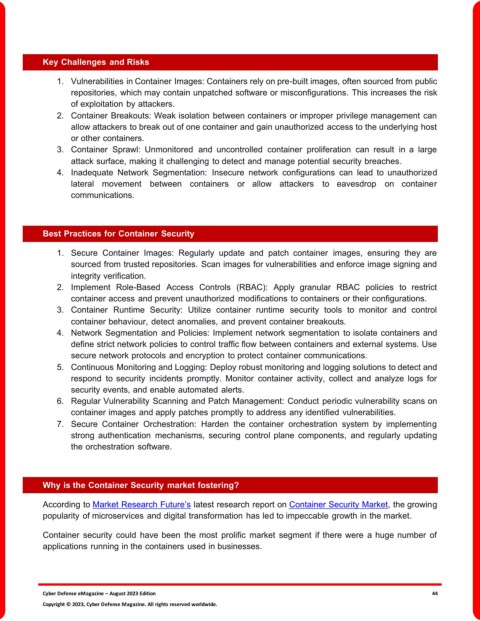
Key Challenges and Risks
1. Vulnerabilities in Container Images: Containers rely on pre-built images, often sourced from public
repositories, which may contain unpatched software or misconfigurations. This increases the risk
of exploitation by attackers.
2. Container Breakouts: Weak isolation between containers or improper privilege management can
allow attackers to break out of one container and gain unauthorized access to the underlying host
or other containers.
3. Container Sprawl: Unmonitored and uncontrolled container proliferation can result in a large
attack surface, making it challenging to detect and manage potential security breaches.
4. Inadequate Network Segmentation: Insecure network configurations can lead to unauthorized
lateral movement between containers or allow attackers to eavesdrop on container
communications.
Best Practices for Container Security
1. Secure Container Images: Regularly update and patch container images, ensuring they are
sourced from trusted repositories. Scan images for vulnerabilities and enforce image signing and
integrity verification.
2. Implement Role-Based Access Controls (RBAC): Apply granular RBAC policies to restrict
container access and prevent unauthorized modifications to containers or their configurations.
3. Container Runtime Security: Utilize container runtime security tools to monitor and control
container behaviour, detect anomalies, and prevent container breakouts.
4. Network Segmentation and Policies: Implement network segmentation to isolate containers and
define strict network policies to control traffic flow between containers and external systems. Use
secure network protocols and encryption to protect container communications.
5. Continuous Monitoring and Logging: Deploy robust monitoring and logging solutions to detect and
respond to security incidents promptly. Monitor container activity, collect and analyze logs for
security events, and enable automated alerts.
6. Regular Vulnerability Scanning and Patch Management: Conduct periodic vulnerability scans on
container images and apply patches promptly to address any identified vulnerabilities.
7. Secure Container Orchestration: Harden the container orchestration system by implementing
strong authentication mechanisms, securing control plane components, and regularly updating
the orchestration software.
Why is the Container Security market fostering?
According to Market Research Future’s latest research report on Container Security Market, the growing
popularity of microservices and digital transformation has led to impeccable growth in the market.
Container security could have been the most prolific market segment if there were a huge number of
applications running in the containers used in businesses.
Cyber Defense eMagazine – August 2023 Edition 44
Copyright © 2023, Cyber Defense Magazine. All rights reserved worldwide.