Page 196 - Cyber Defense eMagazine Special RSA Conference Annual Edition for 2022
P. 196
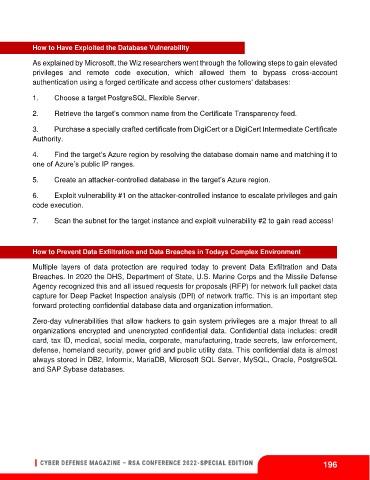
How to Have Exploited the Database Vulnerability
As explained by Microsoft, the Wiz researchers went through the following steps to gain elevated
privileges and remote code execution, which allowed them to bypass cross-account
authentication using a forged certificate and access other customers' databases:
1. Choose a target PostgreSQL Flexible Server.
2. Retrieve the target’s common name from the Certificate Transparency feed.
3. Purchase a specially crafted certificate from DigiCert or a DigiCert Intermediate Certificate
Authority.
4. Find the target’s Azure region by resolving the database domain name and matching it to
one of Azure’s public IP ranges.
5. Create an attacker-controlled database in the target’s Azure region.
6. Exploit vulnerability #1 on the attacker-controlled instance to escalate privileges and gain
code execution.
7. Scan the subnet for the target instance and exploit vulnerability #2 to gain read access!
How to Prevent Data Exfiltration and Data Breaches in Todays Complex Environment
Multiple layers of data protection are required today to prevent Data Exfiltration and Data
Breaches. In 2020 the DHS, Department of State, U.S. Marine Corps and the Missile Defense
Agency recognized this and all issued requests for proposals (RFP) for network full packet data
capture for Deep Packet Inspection analysis (DPI) of network traffic. This is an important step
forward protecting confidential database data and organization information.
Zero-day vulnerabilities that allow hackers to gain system privileges are a major threat to all
organizations encrypted and unencrypted confidential data. Confidential data includes: credit
card, tax ID, medical, social media, corporate, manufacturing, trade secrets, law enforcement,
defense, homeland security, power grid and public utility data. This confidential data is almost
always stored in DB2, Informix, MariaDB, Microsoft SQL Server, MySQL, Oracle, PostgreSQL
and SAP Sybase databases.
196