Page 131 - Cyber Defense eMagazine Special RSA Conference Annual Edition for 2022
P. 131
The Ransomware Encryption Process
Let’s go back to the beginning and discuss how these attacks encrypt systems in the first place.
From the previous ransomware attacks we’ve researched, we learned that from the minute the attackers
get initial access, they can encrypt the entire network in a matter of hours. In other cases, attackers would
spend more time in assessing which assets they want to encrypt and they’d make sure they get to key
servers such as storage and application servers.
Most of the recent ransomware attacks you’re reading about in the news try to terminate antivirus
processes to make sure that their encryption process will go uninterrupted. Recent ransomware variants
such as SNAKE, DoppelPaymer, and LockerGoga even went further by terminating OT-related
processes like Siemens SIMATIC WinCC, Beckhoff TwinCAT, Kepware KEPServerEX, and the OPC
communications protocol. This made sure the industrial process was interrupted, and this increased the
chances that the victims paid the ransom. These types of ransomware attacks were seen in the recent
attacks of Honda and ExecuPharm.
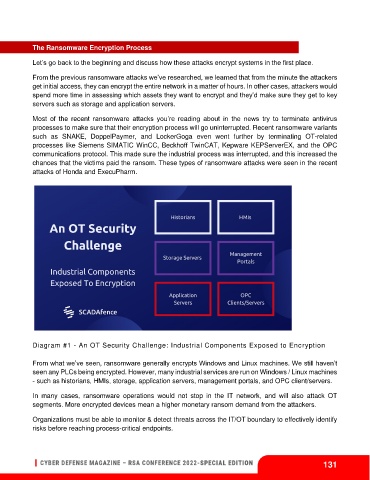
Diagram #1 - An OT Security Challenge: Industrial Components Exposed to Encryption
From what we’ve seen, ransomware generally encrypts Windows and Linux machines. We still haven’t
seen any PLCs being encrypted. However, many industrial services are run on Windows / Linux machines
- such as historians, HMIs, storage, application servers, management portals, and OPC client/servers.
In many cases, ransomware operations would not stop in the IT network, and will also attack OT
segments. More encrypted devices mean a higher monetary ransom demand from the attackers.
Organizations must be able to monitor & detect threats across the IT/OT boundary to effectively identify
risks before reaching process-critical endpoints.
131