Qihoo 360’s Netlab detailed a new evolving DDoS botnet called Abcbot with wormable capabilities that targets Linux systems.
Researchers from Qihoo 360’s Netlab security team have spotted a new botnet, tracked as Abcbot, that targets Linux systems to launch distributed denial-of-service (DDoS) attacks. The security firm analyzed a total of six versions of the botnet to date.
On July 14, 2021, the experts identified an unknown ELF file conducting massive scanning for Linux systems, its analysis revealed it is a Go language implementation of Scanner.
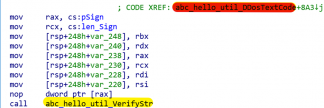
The name Abcbot used to track the bot comes from the source path “abc-hello.”
Errore. Il nome file non è specificato.
The presence of the “dga.go” string in Abcbot’s source path suggests that authors would implement DGA in subsequent versions.
The earliest versions of the malware were very simple, the latest versions (October 30, 2021) target common databases and WEB servers and implement worm-like propagation by leveraging weak passwords and N-day vulnerability.
“At the beginning, Abcbot was relatively simple, and could be seen as a scanner for attacking Linux systems, with a weak password & Nday vulnerability for worm-like propagation.” reads the analysis published by the researchers. “As time passed, Abcbot has continued to evolve, and as we expected, it added the DGA feature in subsequent samples. Today Abcbot has the ability to self-updating, setting up Webserver, laughing DDoS, as well as worm like propagation.”
Components used in the attack chain of this malware family were analyzed in October by Trend Micro, the report detailed attacks against Huawei Cloud to deliver cryptocurrency miners.
Upon installing on a target system, the malware will report the system information to the C2 server, start scanning for open ports to infect other devices, self-update itself when botmasters add new features.
Abcbot leverages the “abc_hello_web_StartServer” function to start a WebServer on the infected systems, listening on port 26800. On October 21, 2021, operators pushed an update to add the open-source ATK rootkit to support DDoS functionality, but it was abandoned with a new update on October 30, 2021, because operators implemented their own DDoS functionality.
“The update process in these six months is not so much a continuous upgrade of features as a trade-off between different technologies,” the analysis concludes. “Abcbot is slowly moving from infancy to maturity. We do not consider this stage to be the final form, there are obviously many areas of improvement or features to be developed at this stage.”
The report also includes Indicators of Compromise (IoCs) for the recent attacks.
Follow me on Twitter: @securityaffairs and Facebook
 Pierluigi Paganini
Pierluigi Paganini
International Editor-in-Chief
Cyber Defense Magazine


