Two security experts have conducted a study that allowed them to spot over 100 snooping Tor Nodes spying on Dark Web Sites.
The attempts of snooping traffic from Tor nodes are not a novelty, in the past, we have reported the activity of threat actors that set up malicious exit nodes to de-anonymize users.
Early 2014, researchers Philipp Winter and Stefan Lindskog of Karlstad University in Sweden identified 25 nodes of Tor network that tampered with web traffic, decrypted the traffic, or censored websites. The experts presented the results of a four-month study conducted to test Tor network exit nodes for sneaky behavior, they discovered that a not specified Russian entity was eavesdropping nodes at the edge of the Tor network.
Now researchers have spotted more than 100 malicious hidden service directories (HSDirs) which are the relays of the network that allow people to visit hidden services.
One year ago the researchers, Filippo Valsorda and George Tankersley presented at the Hack in the Box Security Conference in Amsterdam a de-anonymizing technique leveraging on the analysis of HSDir nodes.
“Since deanonymizing traffic through the entry and exit nodes is so difficult, the researchers began to wonder if there was anything else that sees when a connection happens. The answer: hidden service databases.” reported Idigitaltimes. “When a person wants to host a hidden service, they have to advertise their service on a Tor Onion database, which is a DHT made up of a group of stable relay machines called HSDirs . The person who wants to visit the hidden service has to request information about that service from the database. Therefore, those relays or HSDirs can see who is making the request for a connection and when you want to connect. Therefore, to deanonymize a user’s traffic, an attacker could choose to become the HSDir nodes for the hidden service.”
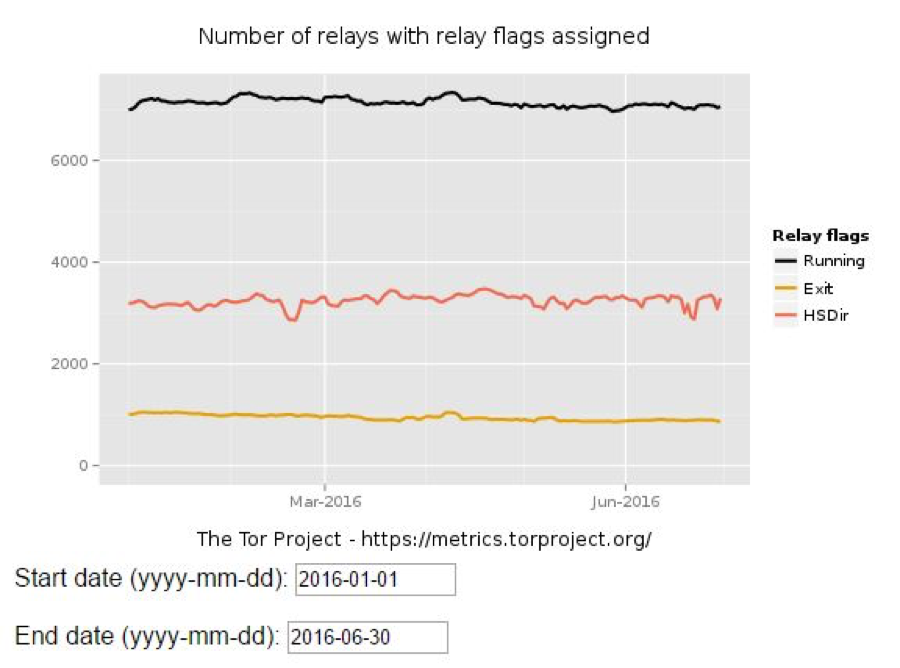
Giving a look to the Tor Metrics published by the Tor Project it is possible to note that there are are over 3,100 nodes with the HSDir flag.

Threat actors abuse of HSDir configuring them to log the addresses of the hidden services. Joseph Cox from Motherboad reported a study conducted by Guevara Noubir, a professor from the College of Computer and Information Science at Northeastern University, and Amirali Sanatinia, a PhD candidate also from Northeaster who revealed the existence of s number of Tor hidden service directories that are spying on Tor websites. Such kind of attacks could allow law enforcement to discover IP addresses of black markets and child pornography sites.
A similar technique could be very useful also for security firms that offer dark web intelligence services.
Threat actors using this technique could reveal the IP address of Tor hidden services, Noubir will present the results of the research at the Def Con hacking conference in August.
“We create what we call ‘honey onions’ or ‘honions.’ These are onion addresses that we don’t share with anyone,” Noubir said.
The security researchers ran 4,500 honey onions over 72 days, they identified that at least 110 HSDirs have been configured to spy on hidden services.
The experts highlighted that some of the threat actors operating the bogus HSDirs were active observers involved in many activities, including penetration testing.
Most of the bogus HSDirs were hosted in the US, followed by Germany, France, but it is impossible to know who really is operating them.