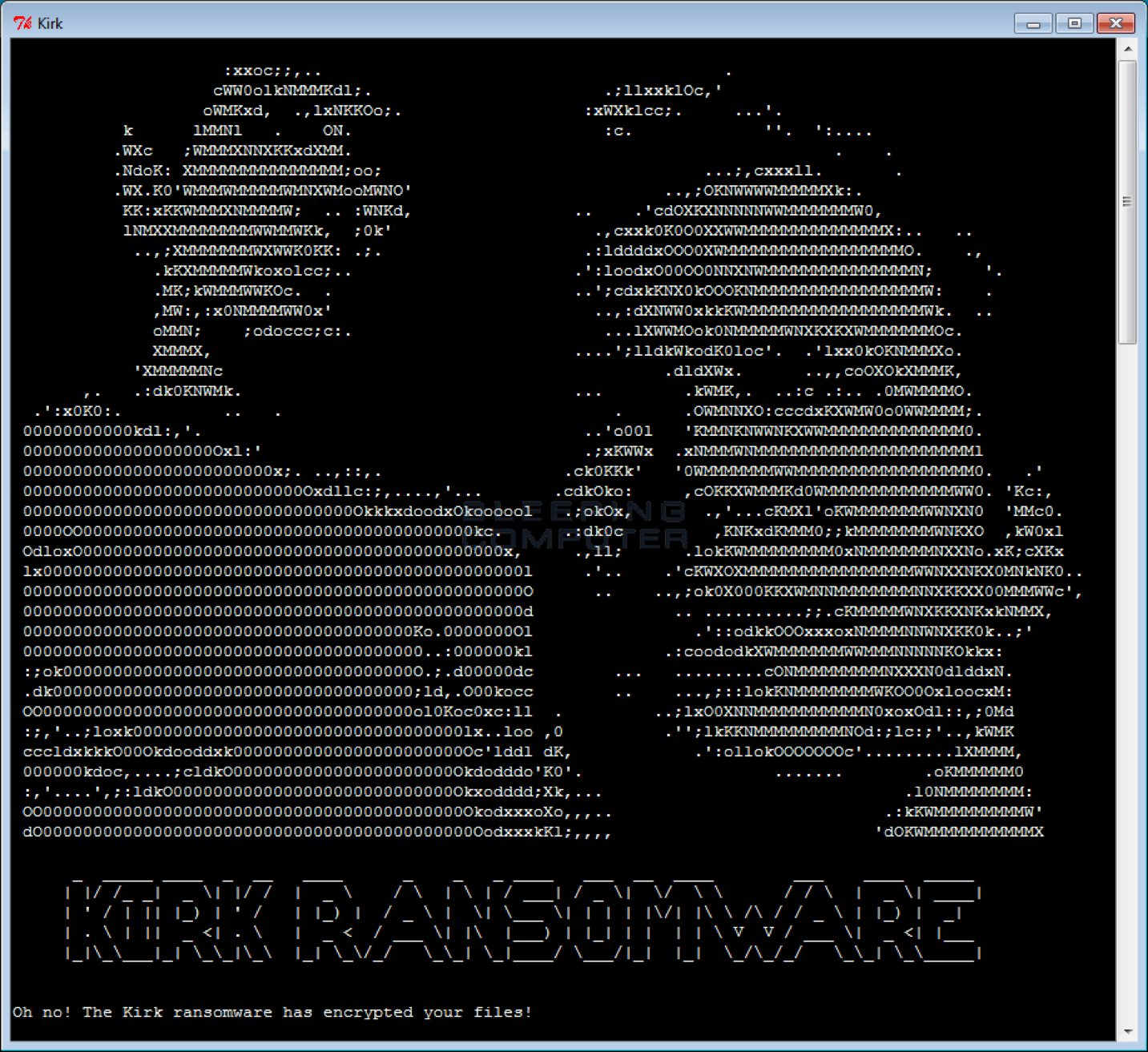
The researchers have discovered a new piece of ransomware featuring a Star Trek theme, dubbed Kirk ransomware, the first one accepting Monero payments.
Ransomware continues to be one of the most profitable cyber threats, for this reason, every week we see new strains of malware in the wild.
The researchers have discovered a new piece of ransomware featuring a Star Trek theme, dubbed Kirk ransomware, that is able to encrypt 625 different file types.
The ransomware appends the. kirk extension to the encrypted file’s name.
The name of the Kirk ransomware is clearly inspired by the name of the popular character in the fiction series Start Trek, such as the name of a decryptor called Spock associated with the threat.

The Kirk ransomware was first discovered by the Avast malware researcher Jakub Kroustek, it is written in Python and is the first ransomware that uses Monero cryptocurrency as the payment currency of choice.
“Discovered today by Avast malware researcher Jakub Kroustek, the Kirk Ransomware is written in Python and may be the first ransomware to utilize Monero as the ransom payment of choice.” wrote Lawrence Abrams from BleepingComputer.
The majority of ransomware in the wild demands Bitcoin payments.
“Even with Bitcoin becoming more accepted, it is still not easy to acquire them. By introducing a new cryptocurrency into the mix, victims are just going to become more confused and make paying ransoms even more difficult.”
The researchers are still investigating the way the Kirk Ransomware is being distributed, they observed it masquerading as the popular network stress tool Low Orbital Ion Cannon.
When the malware is executed it generate an AES key that will be used to encrypt a victim’s files. The AES key will then be encrypted by an embedded RSA-4096 public encryption key and saved in a called ‘pwd‘ that is stored in the directory of the ransomware executable.
The crooks behind the Kirk ransomware ask for this file to be able to provide the victims with the decryptor.
In the same folder, the ransomware drops a ransom note, users are instructed to purchase around $1,100 worth of Monero and send it to a specific address. Once the victim has paid the ransomware then he should send the pwd file and the payment transaction ID to the [email protected] or [email protected] email addresses in order to receive the Spock decryptor.
“At this time there are no known victims of this ransomware and it does not appear to be decryptable,” Abrams added.